Interpersonal Communication in Mediated Contexts
Learning Objectives
- Explain the history of computer-mediated communication.
- Understand the eight (8) concepts describing digital channels.
- Recognize the three specific types of online identities that people can formulate.
- Summarize the main aspects of three (3) CMC theories.
In today’s world, we all spend a lot of time on various devices designed to make our lives easier. From smartphones to social media, we are all in constant contact with family, friends, coworkers, etc. Since the earliest days of communication technologies, we have always used these technologies to interact with one another. This chapter is going to examine technology in our interpersonal relationships.
Technology and Communication
Since the Internet’s creation in 1969, public access to the Internet and the creation of the World Wide Web (www) in 1991, and the proliferation of internet service providers through the late 1990s, the technology that shapes your life today and tomorrow is still relatively new. Here are some relatively recent landmarks in social media sites, technology, and apps: LinkedIn (2003), iTunes (2003), Facebook (2004), YouTube (2005), Twitter (2006), iPhone (2007), Drop Box (2008), Google Docs (2009), Kickstarter (2010), Google+ (2011), Google Glass (2012), Oculus Rift (2013), iWatch (2014), TikTok (2016), BeReal (2020), Chat GPT (2022), Threads on Instagram (2023). As you can imagine, just limiting this list is hard. Some of these products you’re probably very familiar with while others may be new to you altogether.
Development of Computer-Mediated Communication
Before we get started, it’s essential to understand the evolution of what we call computer-mediated communication or CMC. Though some scholars have adopted the broader term “communication technology” in recent years, it may not be necessary because a computer of some kind is always at the center of these communicative interactions.
So what is a computer? In its earliest use, “computers” were people who performed massive amounts of calculations by hand or using a tool like an abacus or slide rule (Figure 1). The idea of “punch cards” would be the basis of many generations of computers until the 1960s. Of course, the punch cards went from being wood cards to cardboard or cardstock throughout its history. Some of the earliest statistical research in the field of communication was conducted using punch cards. The 1970s saw the start of the explosion of the personal computer and the creation of what we now know as the internet. From the 1980s until now, Microsoft and Apple (Macintosh) have cornered the market on personal computers.
Mediation Facilitates Communication
The early Internet was not exactly designed for your regular user, so it took quite a bit of skill and “know how” to use it and find things. Of course, while the Internet was developing, so was its capability for allowing people to communicate and interact with one another. Email was created in 1971 by Ray Tomlinson. Internet forums or message/bulletin boards, which were online discussion sites where people can hold conversations in the form of posted messages. From the earliest days of the Internet, people were using the Internet as a tool to communicate and interact with people who had similar interests.
One early realization about email and message boards is that people relied solely on text to interpret a message with no form of nonverbal communication attached.
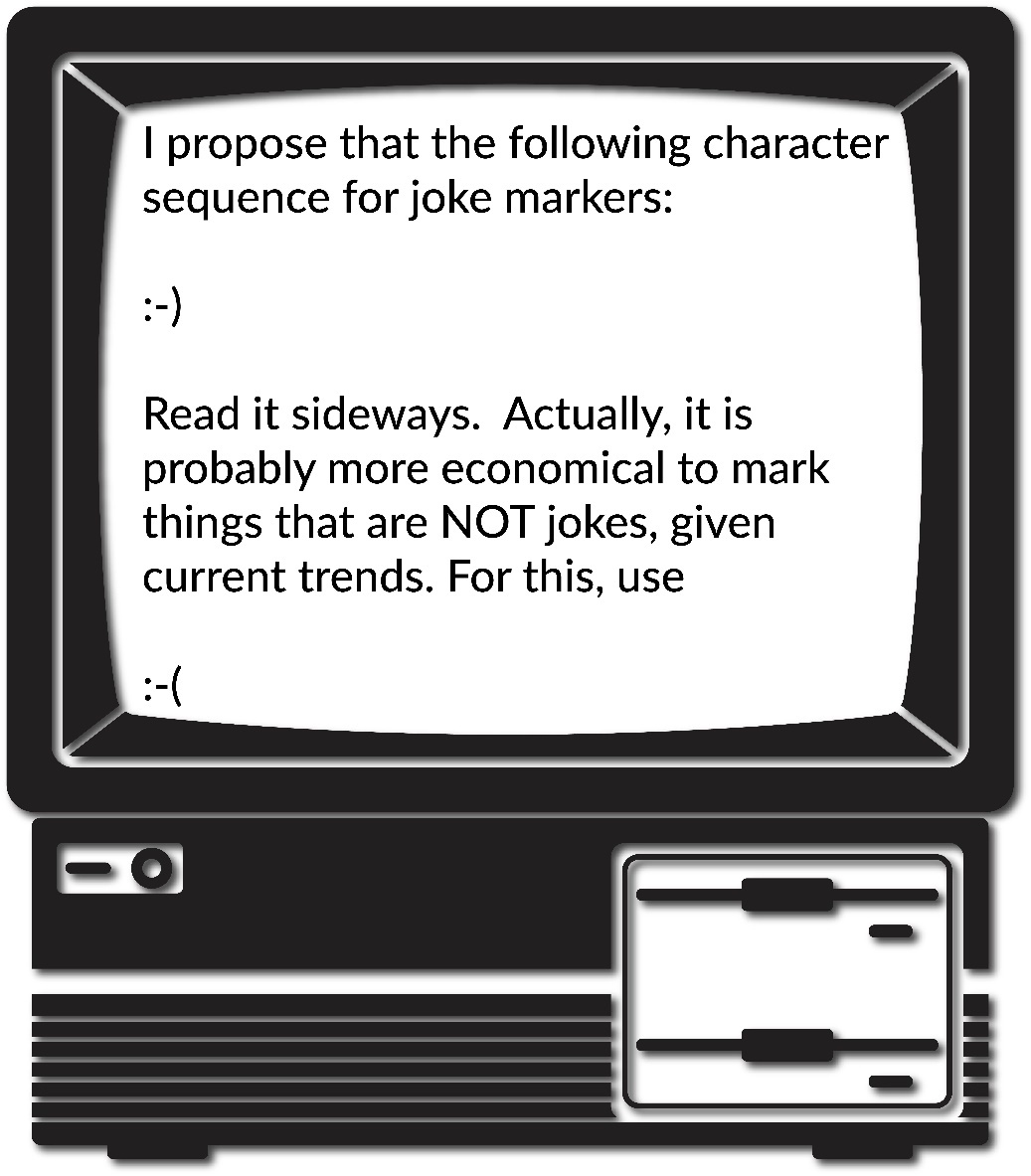
Thus, the emoticon (emotion icon) was born (Figure 1). An emoticon was a series of characters and/or letters designed to help readers interpret a writer’s intended feelings and/or tone. Over the years, many different emoticons were created some useful like the smiley and sad faces. So much of how we understand each other is based on our nonverbal behaviors, so these emoticons were an attempt to bring a lost part of the human communicative experience to a text-based communicative experience.
Information Communication Technology
As technology has developed, our understanding of it has changed. Information Communication Technology (ICTs) describe digital communication options. ICTs consist of technology features and modalities. Modalities or modes are a synonym for communication channels, like text messaging, phone calls, video calls, and email are all unique channels. Features are options within the channel/mode; features may not be available or used by everyone. The ability to turn off or on “read” receipts in a text message is a feature of the texting channel. The ability to flag an email as important is another feature.
Former KU professor, Nancy Baym2, created eight (8) concepts to explain the variability within channels and modes.1 These all exist on a continuum, not a strict binary. Table 1 describes these concepts with examples. Carefully review the table because these eight concepts can be applied to any mode of communication.
1. Synchrony |
Synchronous communication happens in real time. Face-to-face conversations are synchronous, because the communication occurs at the same time. Phone calls and video calls are synchronous channels.
The opposite of synchronous communication is asynchronous, or a mediated form of communication in which the sender and receiver are not concurrently engaged in communication. When Person A sends a message, Person B did not need to be on the computer at the same time to receive the message. There could be a delay of hours or even days before that message received and Person B responded. |
2. Social Cues |
Social cues are nonverbals that can occur thorough a channel. Channels high in social cues allow for multiple nonverbals.
Lean Social Cues: In channels with low social cues, people may do things to supplement that lack. Using emoticons, or emojis, are ways people attempt to create more social cues within a channel. High Social Cues: Video calls allow for each person to visually see the other, hear the emotion and tone of voice, see nonverbal reactions like facial expressions, etc. |
3. Reach |
The concept of reach refers to the number of people who receive a message. Think of reach as the potential number of people your message can reach.
Low Reach A text message to your best friend has low reach. Phone calls typically have low reach, if you are calling one particular person. High Reach An email to your entire class has moderate to high reach. A post on social media can have incredibly broad reach, going “virial” and reaching an immeasurable audience. |
4. Replicability |
Replicability describes how permanent a message can be. If a channel can easily make copies of the same thing, it has more replicability.
A face-to-face interaction is not replicable, because that conversation in that moment in time can never happen again. |
5. Searchability |
The ability to search a channel, often for past communication, is searchability.
Phone calls can show records of when and who called, but not the content of the message. Text messages and emails have higher searchability, as the message content, sender, receiver, and time stamps are recorded. As many of you have likely heard, the internet lasts forever. This is in reference to the replicability of the internet. |
6. Mobility |
How much a channel is connected to a particular place is its range of mobility.
In the past, phone calls were only available on landline phones, connected to one place. With the development and popularization of smartphones, most channels are now highly mobile. |
7. Interactivity |
Interactivity is the amount of social interaction available in a channel.
In the context of interpersonal communication, most of the channels will have high interactivity. |
8. Quantifiability |
This concept refers to the ability to quantify and numerically categorize or count aspects of a channel.
Social media platforms are highly quantifiable, users can see the number of likes, shares, connections, etc. |
Table 1. Eight Concepts of Digital Channels
The CMC Process
As interpersonal communication scholars, our interest in CMC is less about the technologies that people are using and more about how people are using technology to interact with one another. So instead of focusing on how one goes about coding new software, interpersonal communication scholars focus on how new technologies and software help facilitate interpersonal communication. For example, Pat and Sam are playing the latest Massive Multiplayer Online Roleplaying Game (e.g., Word of Warcraft, Fortnite, etc.). As you can see in Figure 5, each player is playing the same video game together but from different locations. Through a technology called VoIP, Sam and Pat can play video games at the same time while talking to each other through the use of headsets.

Synchronous and Asynchronous Communication
In Figure 2, Sam and Pat are in some kind of underworld, fiery landscape. Pat is playing a witch character, and Sam is playing a vampire character. The two can coordinate their movements to accomplish in-game tasks because they can freely talk to one another while playing the game in real-time. As previously discussed, this type of CMC is synchronous communication, or communication that happens in real-time. Conversely, asynchronous communication is communication is the exchange of messages with a time lag. In other words, people can communicate on their own schedules as time permits instead of in real-time. For example, Figure 3 shows a conversation between two college students. In this case, two college students are using SMS, commonly called texting) to interact with each other. The conversation starts at 2:25 PM. The first person initiates the conversation, but doesn’t get a response until 3:05 PM. The third turn in the interaction then doesn’t happen until 5:40 PM. In this exchange, the two people interacting can send responses at their convenience, which is one of the main reasons people often rely on asynchronous communication. Other common forms of asynchronous communication include emails, online discussion forums, company message boards, etc.
Nonverbal Cues
One important difference between face-to-face interaction and CMC is nonverbal communication. Historically, most of the mediums people used to interact with one another were asynchronous and text-based. As such, it was more difficult to ascertain the meaning behind a string of words fully. Culnan and Markus believed that the functions nonverbal behaviors meet in interpersonal interactions simply go unmet in CMC.7 As such, they argued interpersonal communication must always be inherently impersonal when it’s conducted using computer-mediated technologies. This perspective, called the cues filtered out perspective, has three underlying assumptions:
- Communication mediated by technology filters out communicative cues found in FtF interaction,
- Different media filter out or transmit different cues, and
- Substituting technology-mediated for FtF communication will result in predictable changes in intrapersonal and interpersonal variables.8
Let’s breakdown these assumptions. First, CMC interactions “filter out” communicative cues found in FtF interactions. For example, if you’re on the telephone with someone, you can’t see their eye contact, gestures, facial expressions, etc.… If you’re reading an email, you have no nonverbal information to help you interpret the message because there is none. That’s what is meant by nonverbal cues that have been filtered out. For now, we’re going to stop our discussion about nonverbal communication because we will revisit this information later in this chapter when we look at a range of theories related to CMC.
Even if we don’t have the nonverbals to help us interpret a message, we interpret the message using our perceptions of how the sender intended us to understand this message, which can often be wrong. How many times have you seen an incorrectly read text or email start a conflict? Of course, one of the first attempts to recover some sense of nonverbal meaning was the emoticon that we discussed earlier in this chapter.
CMC Rules and Norms
As with any type of communication, some rules and norms govern how people communicate with one another. For example, Twitter, now called ‘X,’ has an extensive Terms of Service policy that covers a wide range of communication rules. For our purposes here, let’s examine their rules related to hate speech:
Hateful conduct: You may not promote violence against or directly attack or threaten other people on the basis of race, ethnicity, national origin, sexual orientation, gender, gender identity, religious affiliation, age, disability, or serious disease. We also do not allow accounts whose primary purpose is inciting harm towards others on the basis of these categories.
Hateful imagery and display names: You may not use hateful images or symbols in your profile image or profile header. You also may not use your username, display name, or profile bio to engage in abusive behavior, such as targeted harassment or expressing hate towards a person, group, or protected category.9
This statement is an obvious example of a rule that exists on the X platform. Of course, some have argued that this rule is pretty flexible at times, given the type of hateful political speech that is often posted by different political figures.
In addition to clearly spelled out rules that govern how people communicate via different technologies, there are also norms for how people communicate. A norm, in this context, is an accepted standard for how one communicates and interacts with others in the CMC environment. For example, one norm that can really frustrate people in text-based CMC environments is yelling, or TYPING IN ALL CAPITAL LETTERS. There’s actually not a consensus on when the avoidance of all capital letters as a tool for yelling first happened. We do know that newspapers in the 1880s often used all capital letters to emphasize headlines (basically have them jump off the page). At some point in the early 1980s, using all caps as a form of yelling became quite the norm, which was noted in a message post from Dave Decot in 1984 (Figure 4).10
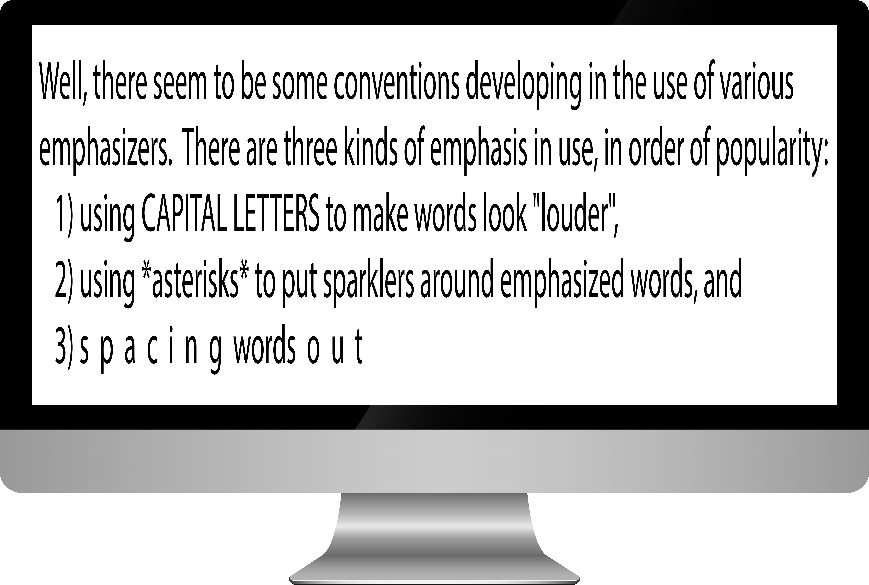
In this example, you see three different attempts to create a system for emphasizing words. The first is the use of all capital letters for making words seem “louder,” which eventually became known as yelling.
Co-Present Interactions & Mediated Communication
Before going too much further into the world of CMC, we need to explain that not everything is great and perfect with the world of CMC interactions. For this discussion, we need to focus on the idea of co-present interactions, or when people are physically occupying the same space while interacting with one another. Historically, most of interpersonal communication involved co-present interactions. With the advent of a range of communication technologies, people don’t necessarily have to be co-present to interact. On the flip side, there are many people who are co-present who use their mediated devices as a way of avoiding FtF interactions with those around them. One of our professor friends recently remarked, “when I started my career, I always had to tell students to quiet down at the beginning of class. Now, they’re already quiet because they’re all looking at their cellphones ignoring those around them.”
Now we often have to encourage collocated social interactions, or how do we get people sitting next to each other to talk to one another. Olsson and colleagues argues that there are two basic problems facing people today, “(1) the use of current technology disrupting ongoing social situations, and (2) lack of social interaction in collocated situations where it would be desirable.”25 When people don’t interact with one another, they tend to become more socially isolated and lonely, which can lead to a true feeling of disengagement with those around them.
How many times have you seen people eating out together yet spending their whole time on their smartphones checking email or texting? Many people believe that this type of multitasking actually enhances productivity, but research tends to disagree with this notion. One study actually demonstrated that when people are confronted with constant distractions like phones ringing or email alerts chiming on a smartphone, people lose an average of 10 IQ points due to these distractions.26 This drop in IQ is equivalent to missing an entire night of sleep. Furthermore, those generations that have grown up with technology are more likely to engage in multitasking behavior.27 In a 2014 study conducted by Jonathan Bowman and Roger Pace, the researchers tested the impact that cell phone usage vs. FtF conversations had while performing a complex cognitive task.28 Not surprisingly, individuals who interacted via cell phones were less adept at performing the task than those engaged in FtF interactions. Furthermore, individuals involved in the FtF interactions were more satisfied with their interactions than their peers using a cellphone. As the authors of the article note, “People think they are effectively communicating their message while dual-tasking even though they are not.”29
So how can technology benefit social interactions? In the Olsson et al. study, the researchers examined several different studies that were designed to help foster collocated social interactions.30 Table 2 illustrates the basic findings from their study.
| Olsson, T. et al. (2020). Technologies for Enhancing Collocated Social Interaction: Review of Design Solutions and Approaches. Computer Supported Cooperative Work, 29, 29–83. https://doi.org/10.1007/s10606-019-09345-0. CC-BY | ||
| Role of technology | Social design objectives | Design approaches |
|---|---|---|
| Enable (previous work beyond which the reviewed literature explores) | ||
| Facilitate |
|
|
| Invite |
|
|
| Encourage |
|
|
Table 2 Mapping the social design objectives and design approaches interpreted from the papers to abstract enhancement categories (Roles of Technology)
In Table 2 you are introduced to four different ways that technology can help facilitate collocated social interaction. You are also presented with the design objectives for each of these different ways to encourage collocated social interaction along with specific design approaches that creators can use to help foster collocated social interaction.
Key Takeaways
- Synchronous communication, or communication that happens in real-time; whereas, asynchronous communication is communication is the exchange of messages with a time lag.
- Nonverbal behaviors are not inherent in many forms of computer-mediated communication. With text-based messages (email, texts, IRC, etc.), there are no nonverbal cues to attend to at all. In other mediated forms (e.g., Skype, Facetime, etc.), we can see the other person, but it’s still not the same as an interaction in a FtF context.
Creating and Recreating the Self Online
Earlier in the book, we discussed the world of intrapersonal communication. At the beginning of this chapter, we had you describe yourself by answering the question, “Who am I?” 20 different times. Look back at that list. Now, think about yourself in the CMC context. Are you the same person in a FtF interaction as you are in a CMC interaction? Maybe, but maybe not. For example, maybe you’re a very shy person in FtF interactions, and you have problems talking with complete strangers online. However, maybe you’re a very quiet person in FtF interactions, but when you’re playing World of Warcraft, you suddenly become very loud and boisterous. One of the beautiful things about CMC for many people is that they can be almost anyone or anything they want to be online. In this section, we’re going to examine some specific factors related to one’s online self. Many social psychologists over the years have attempted to define and conceptualize what is meant by the term “identity.”
Types of Online Identities
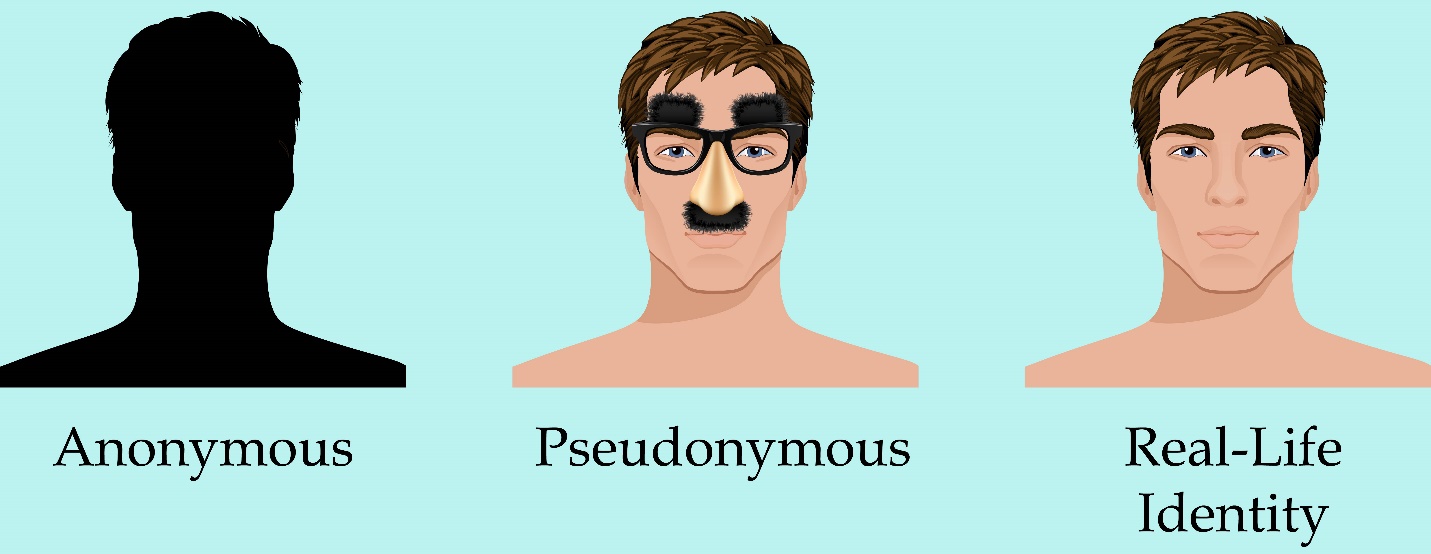
Unlike traditional FtF interactions, online interactions can go even further blurring the identities as people act in ways impossible in FtF interaction. Wood and Smith discussed three different ways that people express their identities online: anonymity, pseudonymity, and ‘real-life’ (Figure 5).47
Anonymous Identity
First, people in a CMC context can behavior in a way that is completely anonymous. In this case, people in CMC interactions can communicate in a manner where their actual identity is simply not known. Now, it may be possible for some people to figure out who an anonymous person is (e.g., the NSA, the CIA, etc.), but if someone wants to maintain her or his anonymity, it’s possible to do so. Think about how many fake Facebook, X, Tinder, Grindr accounts exist. Some exist to try to persuade you to go to a website (often for illicit purposes like hacking your computer), while others may be attempting “catfishing” for the fun of it.
Catfishing is a deceptive activity perpetrated by Internet predators where they fabricate online identities on social networking sites to lure unsuspecting victims into an emotional/romantic relationship. Many of us have seen the MTV show Catfish. The premise of the show repeats, over the course of months, the two exchange more 1,000s of messages, two people fall for one another, but one is not who they seem. Catfish usually begins when one partner starts noticing inconsistencies in various stories that are being told. Catfish-style stories easily reveal the problems that can arise from anonymity on the Internet. Often behavior that would be deemed completely inappropriate in a FtF encounter suddenly becomes appropriate because it’s deemed as “less real” by some.
One of the major problems with anonymity online has been cyberbullying. Teenagers today can post horrible things about one another online without any worry that the messages will be linked back to them directly. Unlike bullying that happened at school, teens facing cyberbullying cannot even find peace at home because the Internet follows them everywhere. It’s also important to understand that cyberbullying isn’t just a phenomenon that happens with children. In a 2009 survey of Australian Manufacturing Workers’ Union members, they found that 34% of respondents faced FtF bullying, and 10.7% faced cyberbullying. All of the individuals who were targets of cyberbullying were also ones bullied FtF.49
Pseudonymous Identity
Second, the second category of interaction is pseudonymity CMC identity. Wood and Smith used the term pseudonymous because of the prefix “pseudonym,” “Pseudonym comes from the Latin words for ‘false’ and ‘name,’ and it provides an audience with the ability to attribute statements and actions to a common source [emphasis in original].”50 Whereas an anonym allows someone to be completely anonymous, a pseudonym “allows one to contribute to the fashioning of one’s own image.”51
There are many famous people who use pseudonyms in their social media: @MrBeast (American YouTuber, internet personality, and businessperson, Jimmy Donaldson), @pewdiepie (online personality and producer Felix Arvid Ulf Kjellberg), @baddiewinkle (Octogenarian fashionista and online personality Helen Van Winkle), @doctor.mike (Internet celebrity family practitioner Dr. Mike Varshavski), etc…. Some of these people used parts of their real names, and others used complete pseudonyms. All of them have enormous Internet followings and have used their pseudonyms to build profitable brands. So, why do people use a pseudonym?
The veneer of the Internet allows us to determine how much of an identity we wish to front in online presentations. These images can range from a vague silhouette to a detailed snapshot. Whatever the degree of identity presented, however, it appears that control and empowerment are benefits for users of these communication technologies.52
Now, some people adopt a pseudonym because their online actions may be “out of brand” for their day-job or because they don’t want to be fully exposed online.
‘Real Life’ or Offline Identity
Lastly, some people have their ‘real-life’ identities displayed online, that is their online identity is very close to the identity they share offline. First, a caveat, it would be inappropriate to say that online identities are not ‘real-life’ certainly a Facebook profile, dating account, or your Snapchat story are all part of your actual, very real, life. You can find JasonSWrench on Facebook, Instagram, Snapchat, Twitter, LinkedIn, etc…. Our coauthor made the decision to have his social networking site behavior very public from the beginning. Part of that reason was that when he first joined Facebook in 2007, he was required to use his professional school email address that ended with.edu. In the early days, only people with.edu email addresses could join Facebook. Jason also realizes that this behavior is a part of his professional persona, so he doesn’t put anything on one of these sites he wouldn’t want other professionals (or even you) to see and read. When it comes to people in the public eye, most of them use some variation of their real names to enhance their brands. That’s not to say that many of these same people may have multiple online accounts, and some of these accounts could be completely anonymous or even pseudonymous.
Online Impression Formation
In the 21st Century, so much of what we do involves interacting with people online. How we present ourselves to others through our online persona is very important (impression formation). How we communicate via social media and how professional our online persona is can be a real determining factor in getting a job.
In today’s world, anything you put online can be found by someone else. According to the 2018 CareerBuilder.com social recruiting survey, in a survey of more than 1,000 hiring managers, 70% admit to screening potential employees using social media, and 66% use search engines to look up potential employees.19 In fact, having an online persona can actually be very beneficial. Forty-seven percent of hiring managers admit to not calling a potential employee when the employee does not have an online presence. You may be wondering what potential employers are looking for when they checkout people online. The main things employers look for is information to support someone’s qualifications (58%); whether or not an individual has a professional online persona (50%); to see what others say about the potential candidate (34%); and information that could lead a hiring manager to decide not to hire someone (22%).20 According to CareerBuilder.com, here are the common reasons someone doesn’t get a job because of her/his/their online presence:
- Job candidate posted provocative or inappropriate photographs, videos or information: 40 percent
- Job candidate posted information about them drinking or using drugs: 36 percent
- Job candidate had discriminatory comments related to race, gender, religion, etc.: 31 percent
- Job candidate was linked to criminal behavior: 30 percent
- Job candidate lied about qualifications: 27 percent
- Job candidate had poor communication skills: 27 percent
- Job candidate bad-mouthed their previous company or fellow employee: 25 percent
- Job candidate’s screen name was unprofessional: 22 percent
- Job candidate shared confidential information from previous employers: 20 percent
- Job candidate lied about an absence: 16 percent
- Job candidate posted too frequently: 12 percent21
As you can see, what you put online says a lot about you as a person to many organizations, so they are checking the Internet to see what exists about you as a person. The flip of this is that what you have online can also help get you hired. In that same study from CareerBuilder.com, they found that 57% of hiring managers have found information about a candidate online that has solidified their decision to hire that person. Here is a list of what hiring managers found that made them want to hire someone:
- Job candidate’s background information supported their professional qualifications for the job: 37 percent
- Job candidate was creative: 34 percent
- Job candidate’s site conveyed a professional image: 33 percent
- Job candidate was well-rounded, showed a wide range of interests: 31 percent
- Got a good feel for the job candidate’s personality, could see a good fit within the company culture: 31 percent
- Job candidate had great communications skills: 28 percent
- Job candidate received awards and accolades: 26 percent
- Other people posted great references about the job candidate: 23 percent
- Job candidate had interacted with company’s social media accounts: 22 percent
- Job candidate posted compelling video or other content: 21 percent
- Job candidate had a large number of followers or subscribers: 18 percent 22
As you can see, having an online presence is important in the 21st Century. Some people make the mistake of having no social media presence, which can backfire on you. In today’s social media society, having no online presence can look very strange to hiring managers. You should consider your social media presence as an extension of your resume. At the very least, you should have a LinkedIn profile because it is the social networking site most commonly used by corporate recruiters. 23
Key Takeaways
- Andrew F. Wood and Matthew J. Smith discussed three specific types of online identities that people can formulate: anonymity (the person behind a message is completely unknown), pseudonymity (someone uses a pseudonym, but people know who the real person behind the message is), and real-life (when our online and FtF identities are the same).
- Our online identities and offline identities portray different facets of our selves, and people can form meaningful impressions based on what they find online.
Theories of Computer-Mediated Communication
Most of the early work in computer-mediated communication from a theoretical perspective was conducted using old mediated theories created to discuss the differences between print, radio, and television and applying them to the Internet. As such, we don’t see the proliferation of theories. To help us understand the theories of computer-mediated communication, we are going to explore five theories and their implications for CMC.
Social Presence Theory
One major theory that has been used to help explain CMC is social presence theory, originally created by Short, Williams, and Christie.56 Presence is a psychological state of mind and how we relate to technology. When we are truly present, we forget that we are actually using technology. Social presence then is “the degree to which we as individuals perceive another as a real person and any interaction between the two of us as a relationship.”57 Our perceptions of presence are largely based on the degree to which we have the ability to interpret nonverbal cues from the people we are interacting with.
When it comes to CMC, various technologies elicit varying degrees of presence. For example, reading information on a website probably is not going to make you forget that you are reading text on a screen. On the other hand, if you’re engaging in a conversation with your best friend via text messages, you may forget about the technology and just view the interaction as a common one you have with your friend. In essence, people can vary in how they perceive presence. Virtual worlds like SecondLife, VRChat, and World of Warcraft can all elicit presence. Each of these involves a virtual world where people can create avatar and interact in a 3D simulated environment. As virtual reality technology takes hold, and online gaming persists, it’s easy to find online virtual communities that offer a great deal of social presence.
Different virtual worlds have different purposes, but people can find both of them highly present. When students who are not familiar with these virtual worlds enter them, they often have a hard time understanding how people can spend hours upon hours interacting with others within these virtual worlds. To the students, they view this as a “strange” experience and experience no social presence at all. Conversely, to the people who “live” in these virtual worlds regularly, they experience high levels of social presence. We do know that those individuals who report higher levels of social presence tend to have more rewarding online interpersonal interactions and are more likely to perceive themselves as competent communicators within these mediated environments.58 Thus, social presence challenges the cues filtered out notion that CMC does not allow us to experience interpersonal relationships. Instead, social presence theory demonstrates how and why people might feel strong connections to communication partners in mediated contexts.
Media Richness Theory
A second major theory that has been applied to CMC is media richness theory. Media richness theory was first proposed by Daft and Lengel.59 Richness is defined as “the potential information carrying capacity of data.”60 Lengel proposed that media varied in richness depending on how much information is provided through the communication.61 For example, in print media, all you have is text. As such, you have no nonverbal behaviors of the author to help you interpret the words you are reading. With FtF communication, on the other hand, we have the full realm of nonverbal behaviors that we can attend to in an effort to understand the sender’s message. As such, Lengel argued that media escalates in richness in the following order: computer output, formal memos, personal memos, telephone, and FtF. You’ll notice that this perspective on media was originally designed to help individuals understand the media choices used in organizations.
So, where does this leave us with CMC? Well, from the basic ideas of media richness theory, we can ascertain that the richer the media, the less ambiguous a message is for a receiver. The theory argues the more rich an individual perceives a medium, the more likely they are to have successful social interactions online. From an organizational perspective, the richer the medium, the better individuals will be able to accomplish specific tasks when they are at a distance from one another. When it comes to the workplace, the more ambiguous a task is, the more people prefer highly rich media for their interactions.62 Media richness is perhaps the most researched CMC theory, but the results are mixed. Mostly the theory is supported, the more ambiguous the task, the more likely someone is to use a rich media, the more clear cut the more likely they’ll use lean media. Sometimes people use lean media to convey a lot of information (e.g., a long email, or this textbook), other times people use really rich media to convey very limited information (e.g., a colleague stops by to ask if you’re going to an event, your parent calls to tell you they paid your tuition.) Either way, the concepts of rich and lean media are important and helpful to understanding how people use media.
Social Information Processing Theory
The first two theories we examined were theories originally designed to examine media before CMC was available to nearly everyone. The first truly unique theory designed to look at CMC from a communication perspective came from Joseph Walther back in 1992 in his social information processing theory.63 As a communication scholar, Walther realized that interpersonal interactions change over time. Some of the other theories really didn’t take into account how interpersonal relationships evolve as the interpersonal interactants spend more time getting to know one another. The two previous theories applied to CMC do not take into account how our impressions of those we interact with can change over time. For example, both media richness and social presence theory focus on the nonverbal aspects and assume that because of the lack of nonverbal cues in CMC, people will inherently find CMC as either less rich or less present when compared to FtF interactions. Walther argued that the filtering out of nonverbal cues doesn’t hurt an individual’s ability to form an impression of someone over time in a CMC context. Ultimately, Walther argues that over time relationships formed in a CMC context can develop like those that are FtF. He does admit that these relationships will take more time to develop, but that they can reach the same end states as those relationships formed FtF.\
From Social to Hyperpersonal
Walther later expanded his ideas of social information processing to include a new concept he dubbed hyperpersonal interactions.64 Hyperpersonal interactions are those that exceed those possible of traditional FtF interactions. For example, many people who belong to online self-help groups discuss feelings and ideas that they would never dream of discussing with people in an FtF interaction unless that person was their therapist. Furthermore, during CMC interactions an individual can refine her or his message in a manner that is impossible to do during an FtF interaction, which will help present a specific face to an interactant. I’m sure we’ve all written a text, Facebook post, or email and then decided to delete what you’d just written because it was in your best interest not to put it out to the world. In CMC interactions, we have this ability to fine-tune our messages before transmitting; whereas, in FtF messages, once something has been communicated, there is no ability to refine the message.
In addition to extended interaction time, the premise of social information processing theory, there are four components of the hyperpersonal theory that explain why people have interactions exceeding the personal-nature of in-person communication. First, the sender has the ability to carefully craft and edit their messages before sending them. This selective self-presentation allows the sender to highlight positive aspects of themselves and omit less desirable traits, creating an idealized version of themselves that may not be as easily maintained in face-to-face interactions. Second, the receiver often fills in the gaps of missing information with their own interpretations, which can lead to over-attribution of similarity. Because the receiver has limited nonverbal cues to rely on, they may assume the sender shares more in common with them than they actually do, further enhancing the hyperpersonal connection. Third, the channel used in computer-mediated communication (CMC) allows for asynchronous interaction, giving both the sender and receiver time to process and respond thoughtfully. This increased control over the timing and content of messages can lead to more intimate and revealing exchanges than might occur in real-time, face-to-face conversations. Finally, feedback effects play a crucial role in reinforcing hyperpersonal interactions. Positive feedback loops occur when the receiver’s idealized perceptions of the sender are confirmed, leading the sender to continue presenting themselves in ways that align with these perceptions. This reciprocal cycle can deepen the connection, making the interaction feel more personal and intense than it might in a traditional in-person context. Social information processing theory and the hyperpersonal approach remain some of the best and well-researched explanations we have for why people for high quality relationships in CMC contexts.
Key Takeaways
- Social presence theory helps us understand whether or not individuals using CMC technologies perceive the people they are interacting with as “real.” Our perceptions of presence are largely based on the degree to which we can interpret nonverbal cues from the people we are interacting with.
- Media richness theory helps us understand CMC behavior by examining the capacity that people have for data. As media becomes richer and has more nonverbal content, the easier it is for a receiver to interpret the message accurately. As such, the more rich an individual perceives a medium the more likely they are to have successful social interactions online.
- Social information processing (SIP_ theory helps researchers understand the development of interpersonal relationships in CMC contexts. SIP argues that overtime relationships formed in a CMC context can develop like those that are FtF.
Key Terms
anonymous CMC identities
People in CMC interactions can communicate in a manner where their actual identity is simply not known.
asynchronous communication
A mediated form of communication in which the sender and receiver are not concurrently engaged in communication.
catfishing
Deceptive activity perpetrated by Internet predators where they fabricate online identities on social networking sites to lure unsuspecting victims into an emotional/romantic relationship.
co-present interactions
When people are physically occupying the same space while interacting with one another.
emoticon
A series of characters and/or letters designed to help readers interpret a writer’s intended feelings and/or tone.
hyperpersonal
CMC interactions that exceed those possible of traditional FtF interactions.
impression formation
How we present ourselves to others through our online persona.
message/bulletin boards
Online discussion sites where people can hold conversations in the form of posted messages.
pseudonymity CMC identity
Identity that someone takes on that is beyond themself in the creation of CMC messages.
real-life CMC identity
When our CMC identity and our FtF identities are congruent.
richness
The potential information carrying capacity of data.
short message service (SMS)
Communication technology allowing for the exchange of short alphanumeric messages between digital and mobile devices found in phones, the Web, or in mobile communication systems (commonly referred to as “text messaging”).
social presence
The degree to which we, as individuals, perceive another as a real person and any interaction between the two of us as a relationship.
synchronous communication
A mediated form of communication in which the sender and receiver are concurrently engaged in communication.
Chapter Wrap-Up
This chapter explored many of the ways that modern communication technologies help us interact with each other. Whether we’re talking over a headset to someone through our gaming consul or texting our roommate, we use these technologies to communicate with people all the time. The first part of this chapter explored the history of computer-mediated communication, which was followed by a discussion of the process of computer-mediated communication. We then discussed identity formation in virtual environments. We ended the chapter look at four of the most commonly discussed theories related to computer-mediated communication. Hopefully, you realize that this chapter barely scratches the surface when it comes to how people are using technology to create and enhance their interpersonal relationships.
Notes
Online discussion sites where people can hold conversations in the form of posted messages.
A series of characters and/or letters designed to help readers interpret a writer’s intended feelings and/or tone.
a synonym for communication channels, like text messaging, phone calls, video calls, and email are all unique channels
options within a channel/mode, what can be done in the mode.
A mediated form of communication in which the sender and receiver are concurrently engaged in communication.
A mediated form of communication in which the sender and receiver are not concurrently engaged in communication.
The argument that mediated communication (CMC) is inherently impersonal.
When people are physically occupying the same space while interacting with one another.
People in CMC interactions can communicate in a manner where their actual identity is simply not known.
Deceptive activity perpetrated by Internet predators where they fabricate online identities on social networking sites to lure unsuspecting victims into an emotional/romantic relationship.
Identity that someone takes on that is beyond themself in the creation of CMC messages.
How we present ourselves to others through our online persona.
The degree to which we, as individuals, perceive another as a real person and any interaction between the two of us as a relationship.
The potential information carrying capacity of data.
CMC interactions that exceed those possible of traditional FtF interactions.

